A Better Approach to RIA Compliance
Jump To Key Section
KEY TAKEAWAYS
- Discover the annual review essentials
- Find out year-end planning priorities
- Understand the chief compliance officer’s empowerment
If you run or work at an RIA firm, compliance is just part of the deal, whether you like it or not. There are rules to follow, records to keep, and audits to stay ready for. Miss something, and it can turn into a real problem in no time.
The problem is that many firms still handle compliance in a messy, reactive way, spreadsheets everywhere, reminders in everyone’s heads, and a lot of last-minute panic. Early access to advisor compliance guidance resources and a better approach to RIA compliance focus on being organized from the start. It’s about using clear processes and smart tools so compliance fits into daily work instead of constantly interrupting it.
Let’s continue with this article and understand when it’s done right, how it keeps your firm protected without slowing everything down.
Annual Review Essentials
Deep yearly compliance reviews, to assess not only policies but also practical implementation, are essential to continued improvement and evolution.
Gap Analysis Priorities
Firms should concentrate on completing gap analyses, particularly for higher-risk areas (such as data privacy and vendor management), and make sure the controls align with actual practice.
Document the firm’s analyses and remediation efforts to reinforce proactive risk management during examinations.
Quarterly Checkpoints
Set up quarterly checkpoints to adjust priorities for new anti-money laundering regulations.
This enables the embedding of compliance practices in work routines and allows for relatively few surprises during regulatory sweeps.
Cybersecurity Safeguards
Data security programs may come with various components, such as layered technology controls, management of access, penetration testing (using your firm’s tech stack), and incident response plans.
Regulators seek vendor oversight and employee incident-response training simulations.
Access and Testing Protocols
Multi-factor authentication must be implemented on all platforms, and third-party relationships should be audited yearly.
Developing a cybersecurity playbook with escalation guidelines and time to recovery, and running tabletop exercises, can save a business from the operational expenses of a disruption and from more scrutiny being set upon its activities.
AML Program Implementation
The more thorough anti-money laundering/countering the financing of terrorism programs have anti-money laundering/countering the financing of terrorism due diligence of clients at the onboarding stage. They also include risk-based and active transaction monitoring, suspicious activity reporting, and training to provide advisors with red flags to watch for.
Monitoring and Oversight
Use automated methods, rather than depending heavily on manual systems, to identify unusual transaction patterns.
Give board oversight of such programs and evidence of annual assessments of their effectiveness.
By doing this, firms focus on meeting expectations and optimizing for scalable operations.
Marketing Rule Adherence
Limit marketing compliance risks by pre-approving all advisor communications, communications on social media, and customer testimonials.
Utilize templates that manage transparency and your marketing objectives without making unsubstantiated performance claims.
Approval Workflows
Document your approval workflows so you can show compliance when conducting audits.
Train your staff to identify compliant endorsements and compliant versus non-compliant endorsements, particularly for third-party reviews.
Continuous mock reviews strengthen judgment and develop a sense of ownership.
Chief Compliance Officer Empowerment
Develop the Chief Compliance Officer position to make it a dedicated, full-time resource with independent oversight, assigned training budgets, established cross-functional committees for firm-focused problems, and a direct reporting line to senior management.
Resource Allocation
You may wish to outsource testing if you’re not yet able to provide capacity in-house.
But you should still practice internal decision-making.
You can specify performance metrics for the CCO, such as reduced exam deficiencies or increased training completion rates.
This changes compliance from a checkbox exercise to a real value driver.
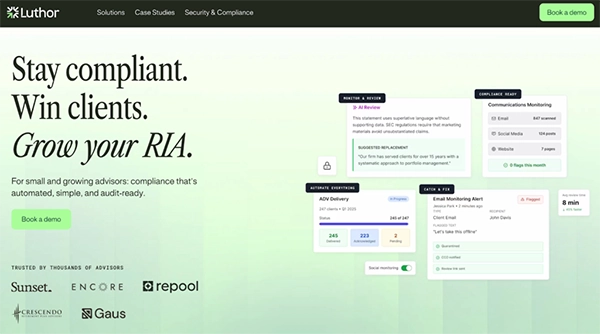
For instance, Luthor.ai is an AI-based tool that can be used to automate routine compliance process tasks like document review.
Recordkeeping Modernization
Upgrade records retention to involve all off-channel communications and electronic communications, more useful archiving of information that should be retained, and automation of retention times for advertisements and client agreements.
Surveillance Integration
Periodic inventories should be undertaken with a look to completeness for all mobile messages.
Recordkeeping and surveillance tools should be combined for real-time anomaly detection.
This acts as a protection against enforcement on incomplete or otherwise inaccessible records.
Vendor Risk Management
Map all third-party relationships and assign risk ratings that depend upon the level of access and criticality.
Require compliance reports, contractually obligated provisions, and yearly attestations from third-party vendors.
Vendor Dashboard
Perform on-site reviews of high-risk partners to validate controls.
Make a vendor dashboard that improves visibility into next renewal dates, incidents, and performance metrics.
This visibility ensures that identity theft prevention standards, among other operational requirements, are appropriately addressed.
Training Program Overhaul
Create live training in appropriate topics, such as rollover recommendations and complicated product disclosures, for staff.
To enhance retention, we administer a quiz after our annual refreshers and separately cater content to advisors vs. operations staff.
Micro-Learning Approach
Monitor both micro-learning and engagement to see how quickly and how well busy teams are completing this learning.
Use completion and feedback to enhance and refresh the program.
Training can bridge knowledge gaps and control inadvertent violations.
Fiduciary Duty Documentation
Standardize documentation of the most suitable interest determinations in retirement advice.
For instance, make suitability, conflicts of interest, and the rationale for client recommendations part of a standardized, account statement-like form.
Conflict Management
Conduct a peer review of high-dollar and complex matters, refresh conflict inventories quarterly, and disclose material conflicts to clients.
This forms a strong case for fiduciary standards, despite the patchwork of state standards and regulations.
Exam Readiness Drills
Simulate regulatory exams on a regular basis with mock audits of advertising reviews, cybersecurity logs, etc.
Establish a team familiar with deficiency letter processes and the timelines for remediating them.
Post-Drill Debriefs
Benchmark against peers with anonymized industry data where applicable.
Debrief after drills and iterate on policies/training to establish a test-every-day mindset.
Readiness makes sure these exams are tools for program validation.
Technology Leverage Tactics
Compliance technology stacks can also assist with surveillance, testing, and reporting as firms grow, and can be integrated via APIs with the business’s customer relationship management (CRM) and trading systems.
Pilot and ROI
Pilot minor solutions like marketing oversight before wider rollout.
Monitor return on investment, e.g., time savings per review or percentage of deficiencies handled.
Built on deliberate use of technology, it overcomes resource limits.
Social Media Compliance Framework
Set up posting guidelines, pick pre-approval queues and archiving methods, and help your consultants get to know the limitations of each platform, like ephemeral stories or direct messaging.
Profile Audits
Execute keyword alerts to catch potentially dangerous content early.
Audit profiles each quarter for compliance, including relevant user engagement analytics.
The framework supports compliant digital outreach in a time of heightened scrutiny.
Policy Testing Protocols
The switch from static policies to dynamic testing regimes that sample activities across risk tiers, check for checklist compliance, and escalate failures for root source analysis is the final option.
Annual Refreshes
Automate wherever possible, e.g., formulaic delivery confirmations.
The yearly policy refreshes should include test results and updates with version control for auditing purposes.
Rigorous testing attests to the program’s vitality.
Year-End Planning Priorities
The next step is to make a compliance calendar outlining the required filings, training cycles, vendor contracts, technology advancements, and any budgeting for an external audit.
Cross-Training
Cross-train backups for essential positions to minimize the impact of turnover.
Recognize and address exam performance themes.
Set numerical goals, such as eliminating the repetition of deficiencies.
Structured planning positions firms for seamless implementation.
Utilizing the following 10 tactics can help RIAs meet regulatory expectations and exceed them.
RIAs can accomplish this through lean principles concentrated on execution, documentation, and flexibility, and by lowering risk for certain high-impact areas of business, such as anti-money laundering readiness and cybersecurity.
Set up the tactics in order, above.
FAQ’s
Ans: The top challenges include cybersecurity/data privacy, complex marketing rules, custody compliance, managing conflicts of compliance, and adopting new technology like AI safety.
Ans: Making RIA compliance easier involves shifting from manual, paper-based processes to automated proactive systems.
Ans: It should be reviewed and updated at least once a year.








